Big, Bureaucratic Companies Aren’t Great at Twitter Social media is a vehicle for snark and wit, something most corporations don’t do...
Big, Bureaucratic Companies Aren’t Great at Twitter Social media is a vehicle for snark and wit, something most corporations don’t do...
Read More
Earlier this year, I recorded an interview on the Small Business Report with Joe Connolly; they reached out to me to discuss a Bloomberg...
Read More
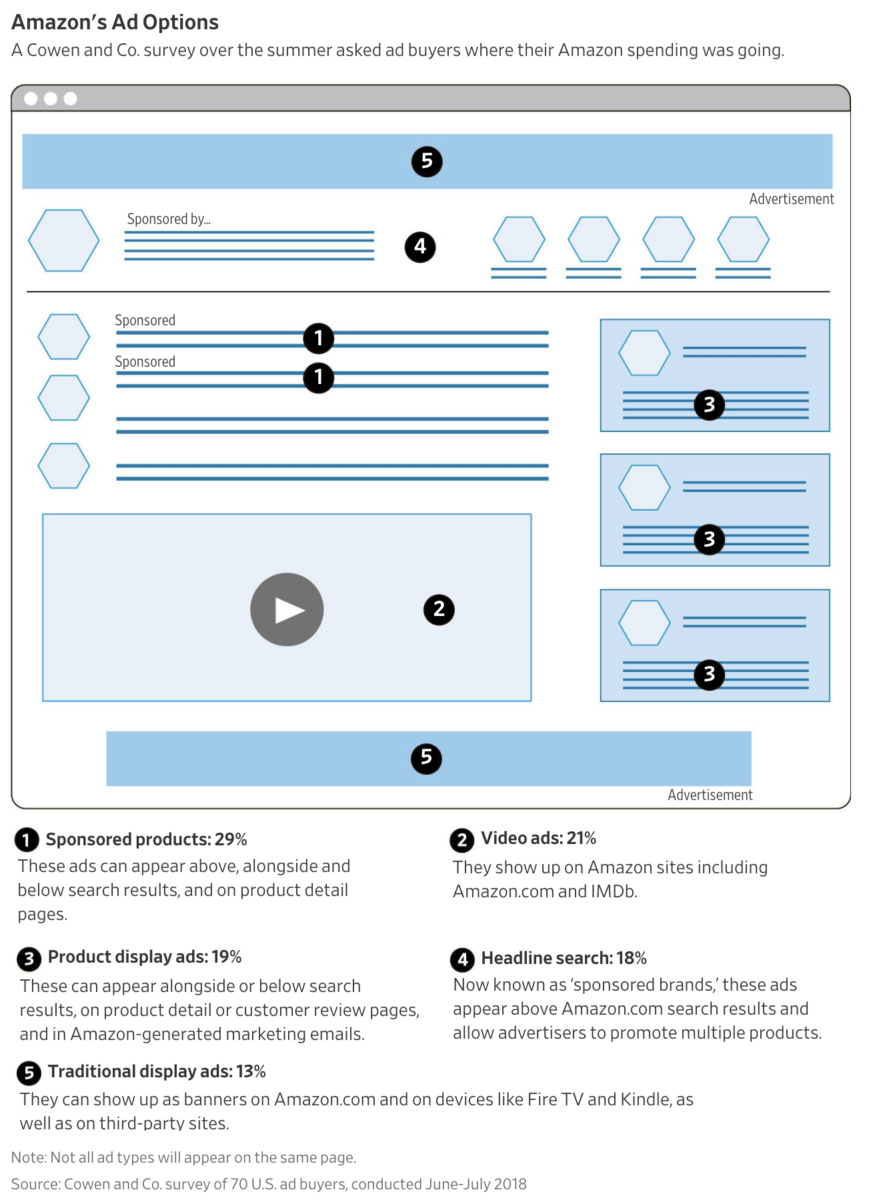
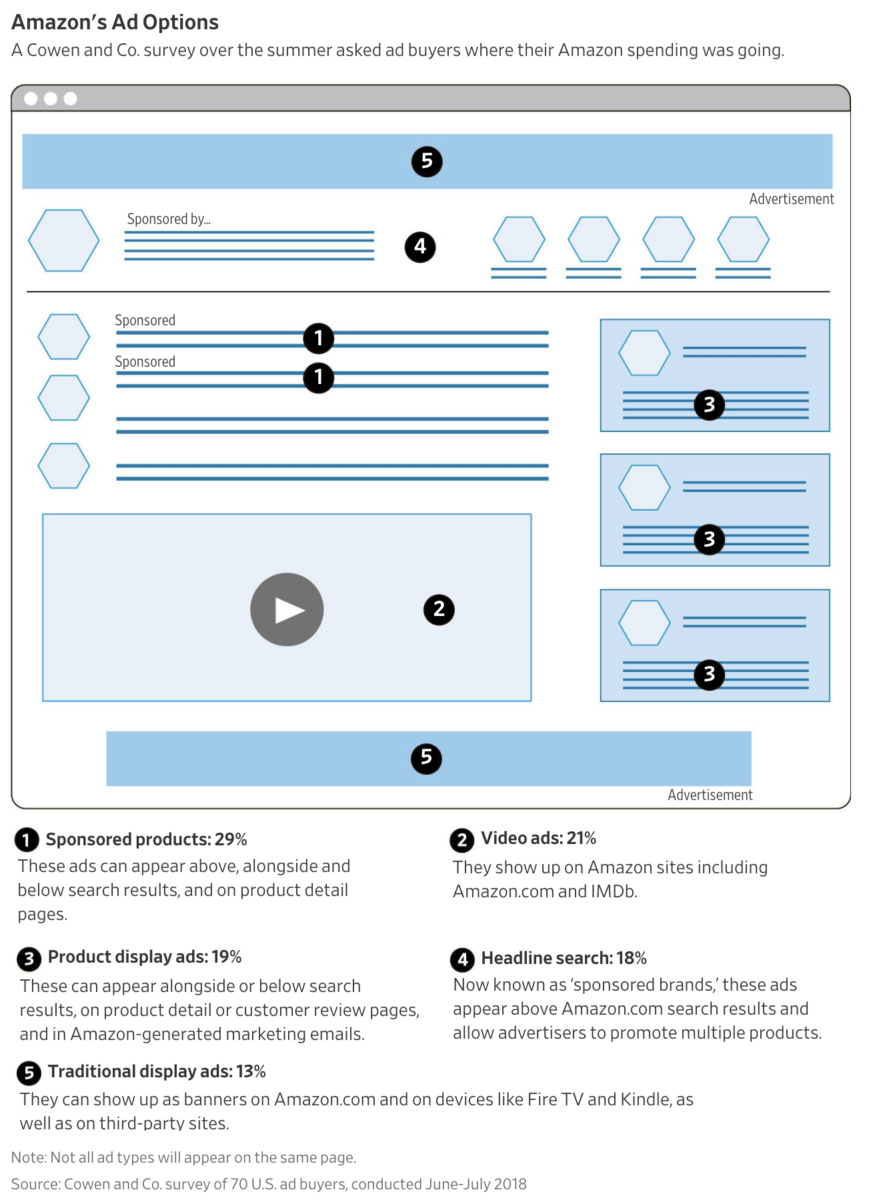 WSJ: “The online retailer has ascended to the No. 3 spot in the U.S. digital ad market behind the dominant...
WSJ: “The online retailer has ascended to the No. 3 spot in the U.S. digital ad market behind the dominant...
Read More
How to Debate Finance Without Being a Jerk A few rules can help prevent financial discussions from becoming as overheated and useless as...
Read More
 All of Trump’s Stock Market Tweets in One Chart Source: Bloomberg
All of Trump’s Stock Market Tweets in One Chart Source: Bloomberg
Read More
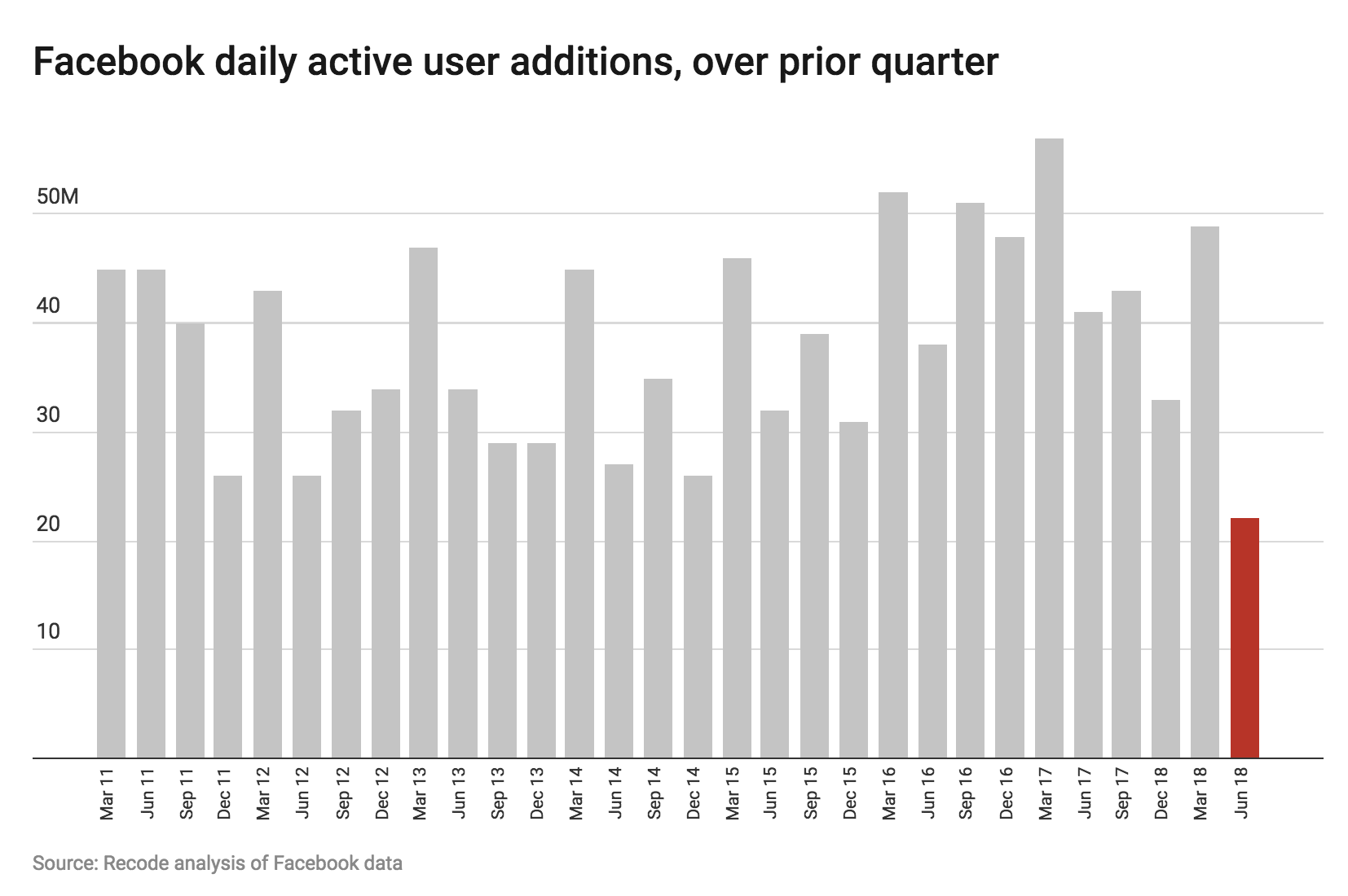
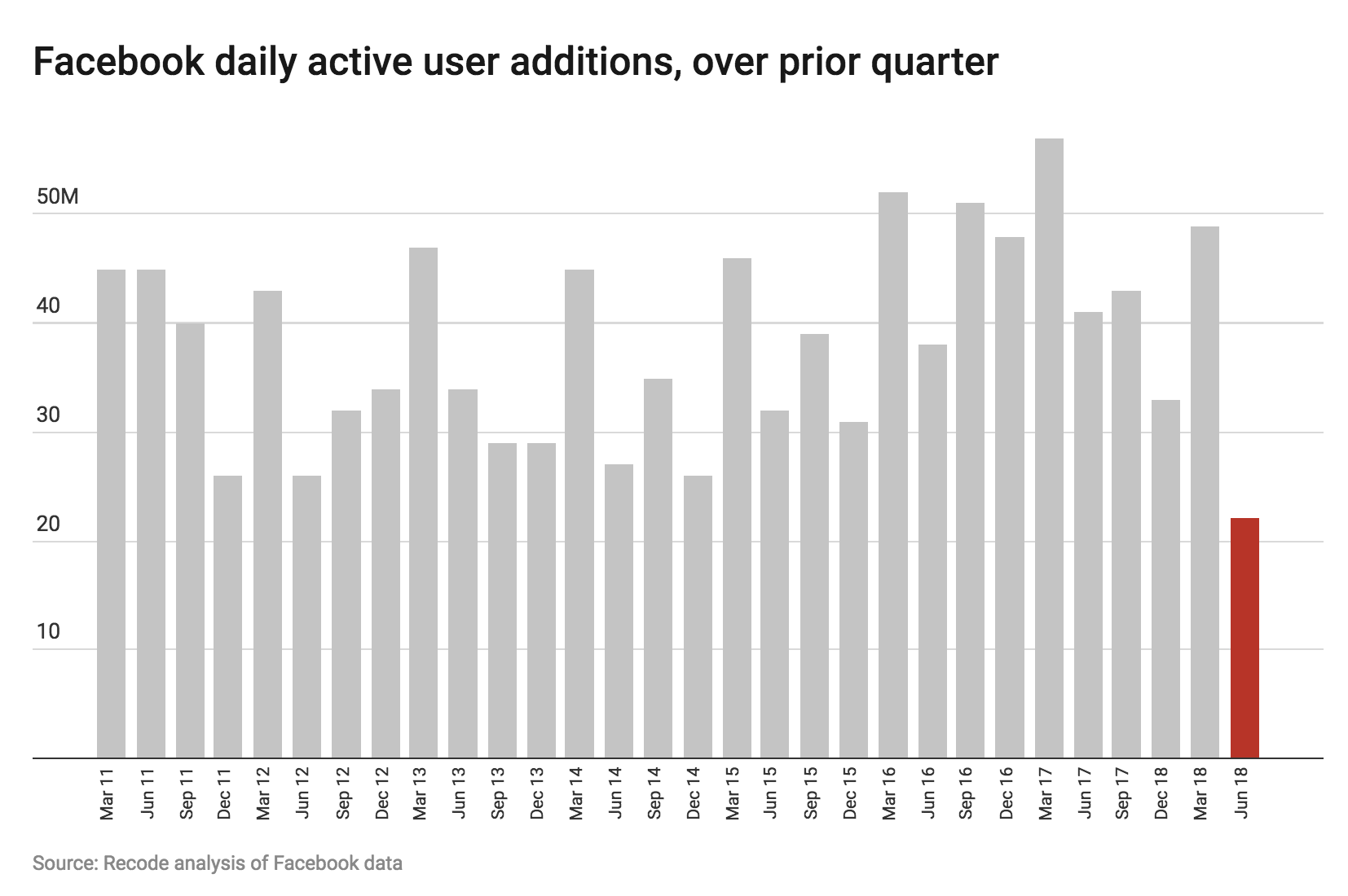 Facebook’s earnings are today after the close. ReCode asks the simple question, “Is Facebook still growing?”...
Facebook’s earnings are today after the close. ReCode asks the simple question, “Is Facebook still growing?”...
Read More
 How to Debate Finance Without Being a Jerk A few rules can help prevent financial discussions from becoming as overheated and useless as...
How to Debate Finance Without Being a Jerk A few rules can help prevent financial discussions from becoming as overheated and useless as...
Read More
What range of ideas are tolerated in public discourse? How and why do previously forbidden ideas and behavior that were once verboten,...
Read More
The transcript from this week’s MIB: Rex Sorgatz and the Encyclopedia of Misinformation is below. You can stream/download...
Read More
This week on our Masters in Business radio podcast, I speak with Rex Sorgatz, who writes about the intersection of technology and...
Read More
 Big, Bureaucratic Companies Aren’t Great at Twitter Social media is a vehicle for snark and wit, something most corporations don’t do...
Big, Bureaucratic Companies Aren’t Great at Twitter Social media is a vehicle for snark and wit, something most corporations don’t do...
 Big, Bureaucratic Companies Aren’t Great at Twitter Social media is a vehicle for snark and wit, something most corporations don’t do...
Big, Bureaucratic Companies Aren’t Great at Twitter Social media is a vehicle for snark and wit, something most corporations don’t do...